I hadn’t originally planned to turn this into a formal project, but as I began collecting artifacts and documenting my findings, it made sense to include it as part of my portfolio. This post includes sample screenshots of the phishing lures, along with attached text-based artifact analysis and a brief report to demonstrate the investigative process and conclusions.
Phishing Email 1 Analysis Contents:
.PDF file for analysis
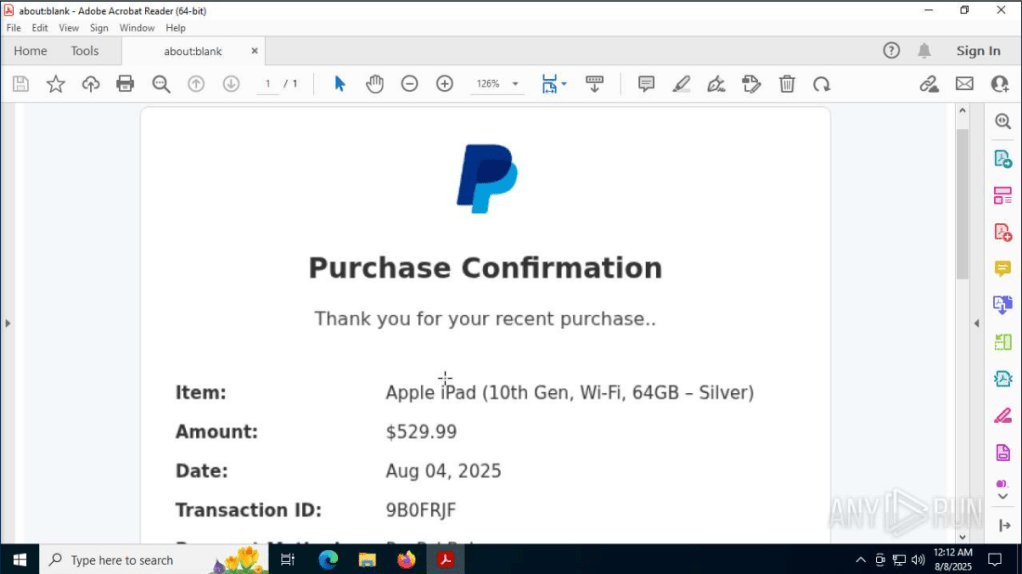
Sample image of phishing attempt – ran through Any.Run
Phishing Email 2 Analysis Contents:
.PDF file for analysis
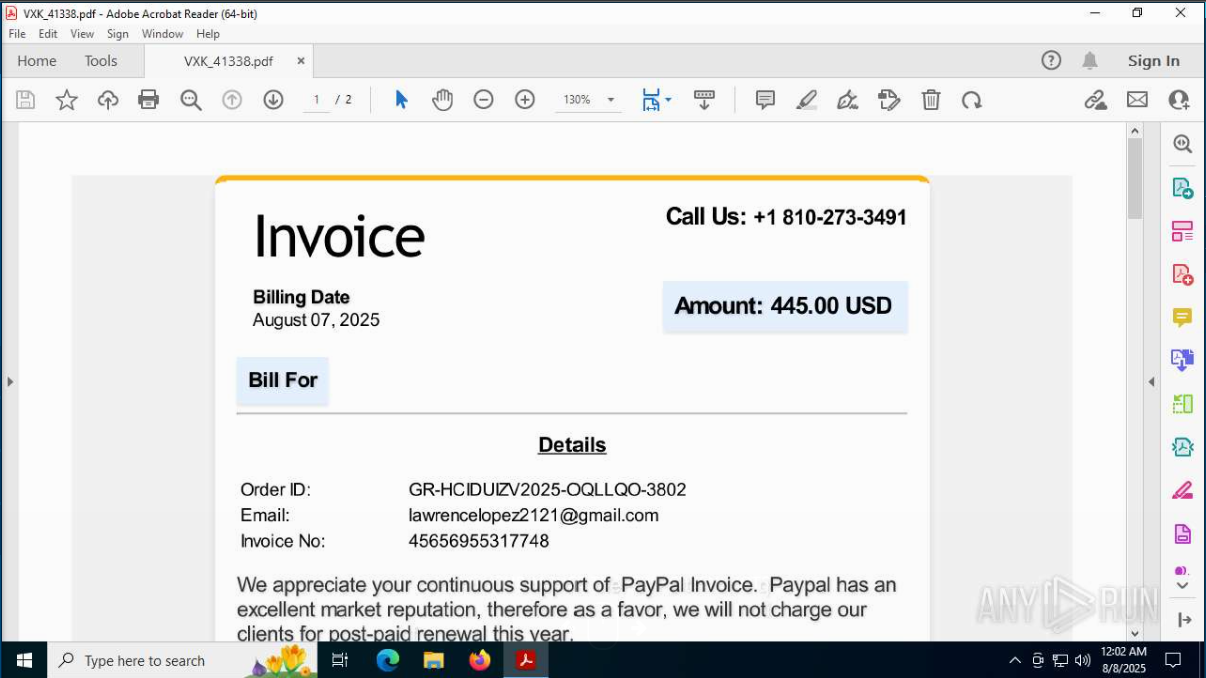
Sample image of phishing attempt – ran through Any.Run
Summary:
Two nearly identical phishing emails were sent to my personal addresses, each impersonating a PayPal purchase receipt. Both urged the recipient to call a listed phone number if the transaction was “unauthorized,” a tactic aimed at harvesting personal or financial information via social engineering. Each message included a PDF attachment mimicking an invoice. Analysis showed no embedded or malicious code — the attacks relied solely on deception rather than technical exploitation. All information was acquired through manual analysis and artifact extraction using Sublime Text, Any.Run, and VirusTotal.
As always, thank you for reading and feel free to reach out!
